Online Cyber Forensics and Investigation Certification in Delhi
CLASSROOM AND ONLINE TRAINING AVAILABLE.
The Bytecode Cyber Security Institute, located in close proximity to Delhi NCR, is currently providing an online cyber forensics investigation course in Delhi that is widely recognized and fully authorized. In the contemporary period, there has been a notable increase in computer crimes within the realm of cyberspace. Numerous criminals are exploiting computer systems and digital devices to perpetrate various forms of both financial and egregious offenses. Law enforcement agencies and governmental bodies are employing computer investigation techniques, while corporate entities, including those operating on a global scale, are increasingly seeking the expertise of Bytecode Cyber Security for our Cyber Forensics Investigation Course in Delhi.

What will you learn in the Online Cyber Forensics Investigation Course in Delhi?
To emphasize the significance of the lucrative online cyber forensics investigator course in the Delhi NCR region, anyone seeking to enhance their knowledge in this field may consider enrolling at Bytecode Cyber Security Institute. This institution boasts a team of highly skilled forensic professionals, each with over eight years of expertise in resolving cases for renowned law enforcement agencies. Moreover, this digital forensics certification curriculum offers a comprehensive understanding of the fundamental principles underlying cyber forensics investigation techniques, which are rarely available elsewhere.
Significantly, this course is well recognized as one of the renowned approved programs in the field of cybercrime investigation. It has garnered praise for its comprehensive curriculum and is delivered by esteemed trainers and mentors, making it a highly esteemed course in terms of knowledge acquisition. The Online Cyber Forensics Training Course offered from the advanced facilities located in Saket and Laxmi Nagar academic branches in New Delhi is designed by industry experts and renowned cyber forensics investigators. The curriculum is carefully tailored to meet the needs of aspiring professionals in this field.
Cybersecurity and Digital Forensics
Bytecode Security has made significant strides in delivering highly trained and proficient cyber forensics experts to diverse law enforcement agencies. In addition, this advanced online cyber investigation training program is well-suited for individuals who are currently enrolled in college as well as professionals seeking to transition into this field or initiate their careers in cyber forensics investigation.
An individual with a genuine desire for education will get the necessary foundational understanding of digital forensics by enrolling in the cyber forensics investigation course offered in the Delhi National Capital Region (NCR). For example, doing a comprehensive analysis and extraction of data from diverse Operating Systems during the forensic phase, retrieving encrypted, concealed, erased, and manipulated data from several storage devices and partitions. The purpose of this action is to get potentially admissible evidence in a court of law while preserving the authenticity of the source.
Cyber Forensics Investigation Online Course
Further, we possess a comprehensive understanding of the time constraints faced by a significant number of our students. As a result, we have developed a distance learning program known as the Cyber Forensics Investigation Online Course, which aims to address these concerns. The Online Digital Forensics Course offers an effective method for students to acquire knowledge and address uncertainties with the guidance of experienced cyber forensics investigators. This is achieved through Virtual Instructor-Led Training (VILT) sessions, which follow the same curriculum as our offline instructor-led training sessions, which are also offered by Bytecode Security at Saket and Laxmi Nagar institutes in Delhi, NCR.
Students can attend classes from their homes. It takes less time to attend an online class. At the same time, various groups can attend online classes with bytecode Cyber Security From home.
OUR CURRICULUM
Module 01: Computer Forensics in today’s World
Module 02: Computer Forensics Investigation Process
Module 03: Hard-Disk and File System
Module 04: Data-Acquisition and Duplication
Module 05: Defeating Anti-Forensics Techniques
Module 06: Windows Forensics
Module 07: Linux Forensics
Module 08: Network Forensics
Module 09: Web Forensics
Module 10: Dark Web-Forensics
Module 11: Cloud forensics
Module 12: Email-Forensics
Module 13: Malware Forensics
Module 14: Mobile forensics
Module 15: IOT Forensics
Course Duration
- Course Duration: 40 Hours
- Course Level: Intermediate
- Included: Training Certificate
- Language: English, Hindi
- Course Delivery: Classroom Training
- Course pdf: Click here to Download
Our Students are Placed in Companies




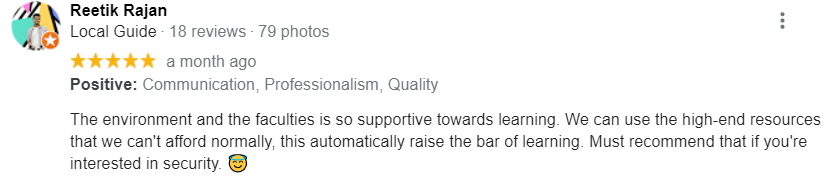
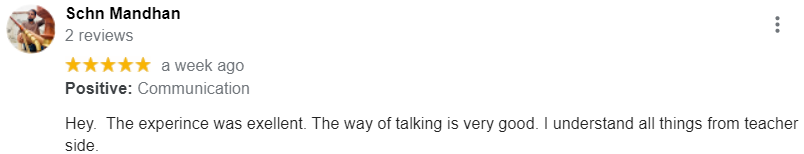
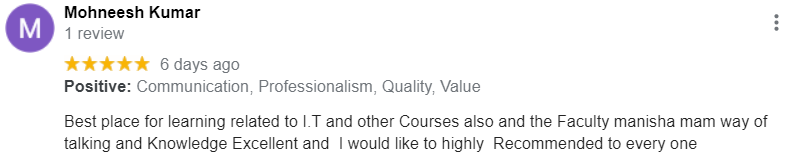
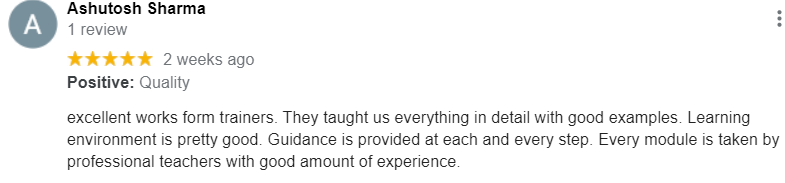
Our Google Reviews
Our Related Course
Frequently Asked Questions
About The Best Cyber Forensics and Investigation Certification Course Program
What are cyber forensics tools?
The following list enumerates the specialized technologies employed by experts in the field of cyber forensics to effectively address complex cybercrime investigations:
- Network Forensic tools.
- Database analysis tools.
- File analysis tools.
- Registry analysis tools.
- Email analysis tools.
- OS analysis tools.
- Disk and data capture.
Which is the first type of forensics tools?
Identification. It is the first step in the forensic process. The identification process mainly includes things like what evidence is present, where it is stored, and lastly, how it is stored (in which format). Electronic storage media can be personal computers, Mobile phones, PDAs, etc.
How does cyber forensics work?
Cyber forensics encompasses a range of methodologies employed by investigators to gather and scrutinize potential evidence found within digital or physical assets. These assets may be subject to manipulation, concealment, encryption, or tampering through the utilization of data obfuscation techniques by malicious actors.
In the field of cyber forensics, data acquisition is carried out with the objective of preserving the integrity of the original data source. This is achieved by the creation of precise replicas of the data resource.
Which tool is needed for a computer forensics job?
Sleuth Kit (+Autopsy) is a Windows-based utility tool that makes forensic analysis of computer systems simpler. This tool allows you to inspect your hard drive and cell phone. Highlights: You can distinguish movement utilizing a graphical interface successfully
How many types of forensics are there?
There are a total of twelve distinct categories of forensic science that are currently available in the market, as enumerated below:
- Computational Forensics
- Forensic Astronomy
- Forensic Geology
- Forensic Seismology
- Digital Forensics
- Forensic Art
- Forensic Entomology
- Bloodstain Pattern Analysis
- Forensic Chemistry
- Election Forensics
- Forensic Engineering
- Forensic DNA Analysis
How long does a forensic investigation take?
The duration of a digital forensics examination typically ranges from 15 to 35 hours. It is worth noting that a comprehensive analysis of 100 GB of data stored on a hard disk can contain over 1,000,000 pages of electronic information. This process typically requires a significant amount of time, ranging from 15 to 35 hours, to compute the results and extract the relevant data that can be deemed acceptable in a court of law. The duration required for examining prospective evidence can exceed 35 hours, contingent upon the dimensions and format of the media being analyzed.
How do I get a job in forensics?
One can acquire a prospective employment opportunity within the realm of Digital Forensics Investigation through the successful completion of a dedicated and authentic Cyber Forensics Investigation Course offered by Bytecode Cyber Security Institution at their Saket and Laxmi Nagar branches. These branches boast highly competent and seasoned instructors in the field of forensics, making them prominent figures in the entire country.
Which software can make a forensic copy of RAM?
There is a wide range of software applications currently available in the industry that possess the capability to accurately replicate Random Access Memories (RAM) through the utilization of distinct approaches. The Digital Evidence Investigator® (DEI) software is the most suitable option for this specific range of functions
What is digital forensics course?
A Digital Forensics Course encompasses a comprehensive collection of tools, methodologies, and concepts that enable individuals to acquire and extract information as tangible evidence, which can be deemed admissible in a court of law to prosecute cybercriminals.
In the same perspective, Bytecode Security provides an advanced Cyber Forensics Investigation Course with highly experienced forensics educators who possess a teaching tenure of nearly 8+ years in the industry.
What is the scope of cyber forensics?
The field of Cyber Forensics is experiencing significant growth due to its crucial role in retrieving admissible facts from digital assets acquired at crime scenes. As global crime rates continue to rise, criminals are increasingly utilizing a wide range of digital tools to perpetrate various forms of cybercrime.
Which is better cybersecurity or digital forensics?
The response is contingent upon the decision made by the user. For individuals with an interest in national service or the resolution of criminal cases, obtaining certification in a Cyber Forensics Training Course presents a mutually beneficial opportunity. Nevertheless, individuals who possess a strong inclination towards identifying weaknesses within an information technology infrastructure may discover that pursuing a career in cyber security aligns with their interests.